Okta Implementation & Identity Services
Okta Implementation Services. Workforce Identity. CIAM. Federal Scale.
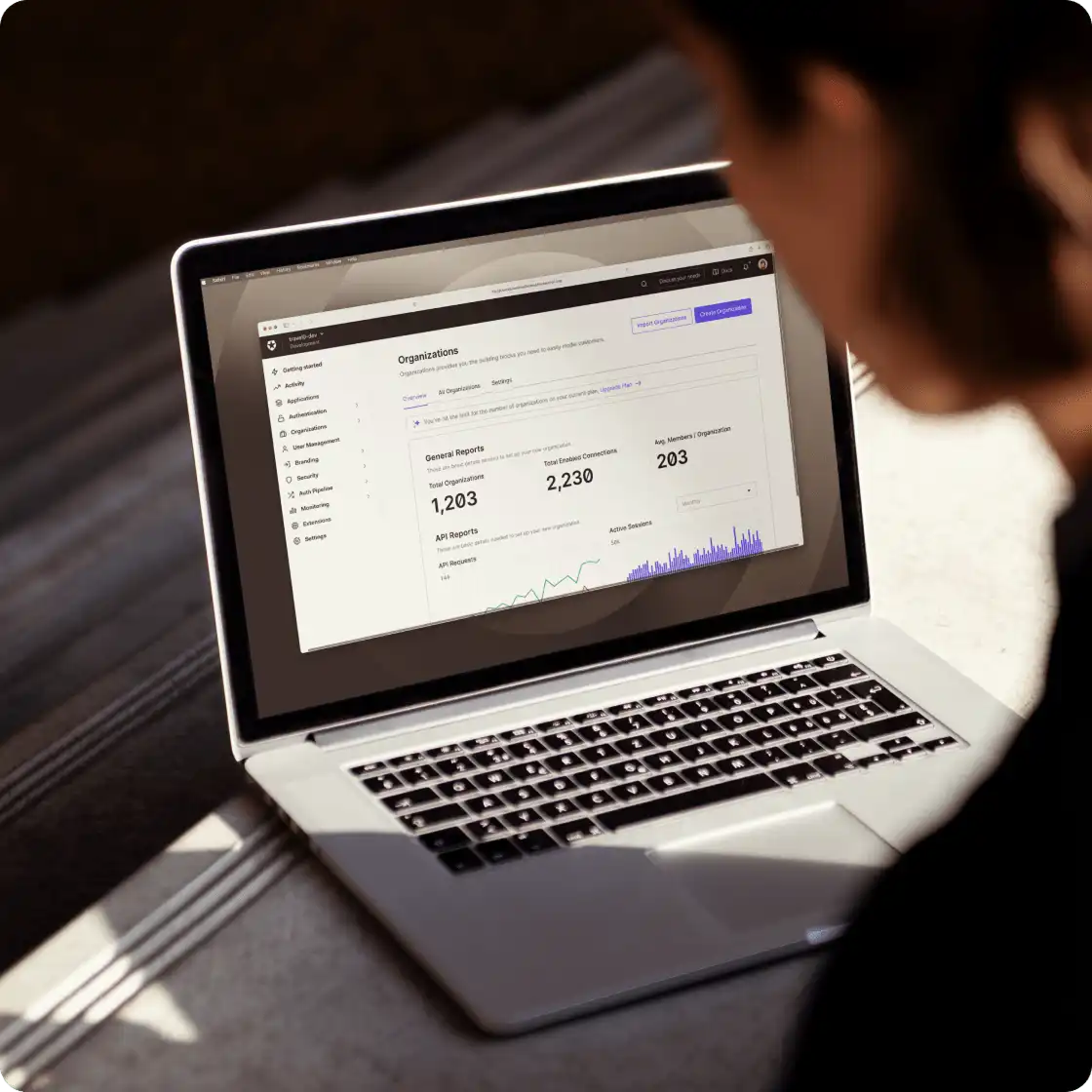
Ridge IT is certified across the full Okta stack — Workforce Identity, CIAM, and Certified Delivery. Our Okta services cover the full lifecycle: we architect, deploy, migrate, and actively manage Okta Workforce and Customer Identity for organizations that can't afford to get identity wrong.
Why Identity Security Can't Wait
What Happens When Identity Controls Fail?
The attacks on Snowflake customers in 2024, the Change Healthcare breach, the AT&T data exposure — all of them started with compromised credentials and missing MFA. These are the numbers behind that pattern.
Why Ridge IT + Okta
What Does Okta Implementation from a Certified Delivery Partner Actually Deliver?
Okta has thousands of resellers. Certified Delivery Partners are different — we've demonstrated the technical depth to architect complex identity environments, migrate production workloads, and manage Okta as an integrated component of a broader security stack. Our Okta delivery practice and Okta services span both Workforce and Customer Identity (CIAM) implementation.
Certified, Not Just Authorized
Our Okta Certified Delivery Partner status validates hands-on deployment expertise across SSO, Adaptive MFA, Lifecycle Management, and Identity Governance. Our engineers hold individual Okta certifications and have shipped Okta deployments at every scale — from 50-user startups to 3-million-user federal agencies.
Okta Is Part of the Stack, Not a Silo
Most Okta deployments stop at SSO and call it done. Ridge IT connects Okta to CrowdStrike Identity Threat Protection and Microsoft Entra ID to create a unified identity control plane. When Okta AI flags an anomaly, it routes to our SOC for real human triage — not a ticket queue.
You Always Own Your Okta Tenant
Ridge IT manages Okta on your behalf — but your Okta tenant, your licenses, and your admin access are always yours. We never hold licenses on behalf of clients. If you ever leave, you take everything with you. No black boxes. No lock-in.
"3 million users. One Okta platform."
A Department of Defense-adjacent agency engaged Ridge IT to consolidate a fragmented identity environment — dozens of legacy directories and authentication systems — onto a single Okta platform. Migrating 3 million enrolled users without disrupting production operations required meticulous phased migration planning, deep Okta delivery expertise, and a disciplined rollout model.
The outcome: unified SSO, consistent Adaptive MFA enforcement, and automated lifecycle management across the entire organization. Legacy directories decommissioned. Audit surface reduced. Identity governance enforced at scale.
Platform Capabilities
What Does Okta Implementation Include? 9 Modules We Deploy and Manage
Okta is more than SSO. Here's a module-by-module breakdown of the Okta services Ridge IT implements, configures, and manages — and why each one matters to your security posture.
Universal Directory
Centralizes user profiles, groups, and device records from Active Directory, LDAP, and other sources. Enables seamless synchronization and attribute mapping across all connected applications.
Single Sign-On (SSO)
Secure one-click access to 7,000+ cloud, on-premises, and mobile applications with a single set of credentials. Significantly reduces password sprawl and reduces help desk load overnight.
Adaptive MFA
Evaluates real-time risk signals — device familiarity, geographic location, behavioral patterns — and dynamically adjusts authentication challenge level. Stops attackers without stopping your team.
Lifecycle Management
Automated provisioning, de-provisioning, and role transitions across every connected application. When someone joins, their access is ready. When they leave, everything is revoked — without a ticket.
Access Governance
Automated access certifications, least-privilege policy enforcement, and periodic reviews. Satisfies the access review requirements in CMMC, PCI-DSS, SOC 2, and FFIEC frameworks.
Privileged Access
Just-in-time admin elevation, credential vaulting, and session monitoring for privileged accounts. Dramatically reduces the blast radius when an admin account is targeted.
Identity Threat Protection
Okta AI continuously monitors for identity anomalies — impossible travel, session hijacking indicators, credential stuffing patterns — and triggers automated response actions.
Identity Security Posture Mgmt
Continuously scans for identity misconfigurations, excessive permissions, and policy drift across all Okta integrations. Surfaces remediation priorities before attackers find them first.
Workflows (No-Code Automation)
No-code platform for building complex identity automation — multi-step approvals, event-triggered access changes, third-party app orchestration. Removes the manual work from identity operations.
Full-Stack Integration
How Does Okta Connect to the Rest of Your Security Stack?
Identity is most powerful when it's connected — not siloed. Ridge IT integrates Okta with the rest of your security architecture so every tool knows who is who, what device they're on, and whether the access should be permitted.
Okta (Identity)
The identity control plane. Every access request is verified against Okta's user profiles, group memberships, and risk signals before being granted. FedRAMP High-authorized for DoD environments.
Zscaler ZPA (Network)
Zero Trust network access. Okta identity signals feed directly into Zscaler ZPA access policies — users only reach the applications their Okta profile permits. No implicit trust based on network location.
CrowdStrike Identity (Detection)
CrowdStrike Identity Threat Detection monitors for lateral movement, privilege escalation, and credential abuse across the entire identity fabric — complementing Okta AI's access-layer detection.
The integration payoff: During the SonicWall breach wave, clients with CrowdStrike Identity Protection watched attackers be stopped in real time — each compromised account was disabled the moment suspicious activity was detected. Clients without identity detection in place got cryptolocked. The difference is whether your identity layer is passive (just SSO) or active (SSO + behavioral detection + human SOC triage).
Customer Identity (CIAM)
Okta Implementation for Customer Identity (CIAM) — Beyond Workforce
Identity isn't just an employee problem. Customer-facing applications need the same rigor — adaptive authentication, self-service registration, progressive profiling, and fraud detection — without killing the user experience. Ridge IT is CIAM-certified and delivers Okta Customer Identity implementations for organizations that need to protect customer accounts at scale.
Customer Registration & Progressive Profiling
Frictionless sign-up flows with progressive data collection. Customers authenticate once and build profiles over time — no form fatigue. Okta handles identity verification, email/phone verification, and social login federation.
Adaptive Authentication for Customer Apps
Risk-based step-up authentication that adjusts challenge levels based on device trust, location anomalies, and behavioral signals. Stops account takeover without punishing legitimate customers.
API Access Management & Token Security
Okta-issued OAuth 2.0 tokens govern API access to your customer-facing services. Ridge IT configures scoped access policies, token lifetimes, and revocation rules aligned to your application architecture.
Ridge IT's Okta services and delivery practice covers both Workforce Identity and Customer Identity — meaning you get a single Okta implementation partner for internal employees, contractors, partners, and customer-facing applications. No handoffs. No second vendor. One team that handles every Okta service from architecture to ongoing management.
Okta Delivery Methodology
How Ridge IT Delivers Okta Implementation — From Assessment to Managed Services
Every Okta implementation follows our crawl, walk, run Okta delivery methodology. We don't over-architect on day one — our Okta services start with what matters most, validate it in production, and expand from there.
Discovery & Assessment
Map existing identity infrastructure, app catalog, user populations, and compliance requirements. Identify gaps, redundancies, and quick wins before touching configuration.
Architecture & Design
Design the Okta tenant structure, authentication policies, lifecycle rules, and integration touchpoints with CrowdStrike, Zscaler, and Microsoft Entra. CIAM flows designed in parallel for customer-facing apps.
Phased Deployment
Pilot group validation → department rollout → full production. Every SSO app connection validated before moving forward. Legacy systems decommissioned only after full verification.
Managed Okta Services
Ongoing Okta administration, policy tuning, user lifecycle automation, access reviews, and SOC-integrated identity threat monitoring. Your tenant. Your licenses. Our expertise.
Inc. Magazine's #1 MSSP. Three Consecutive Years.
Ridge IT Cyber is the top-ranked Managed Security Service Provider on the Inc. 5000 America's Fastest Growing Private Companies list. 700+ organizations protected. 2.5 million+ humans secured. Okta Certified Delivery Partner with proven federal-scale deployment experience.
Side-by-Side Comparison
Okta vs. Microsoft Entra ID — Which Identity Platform Is Right for You?
Most mid-market organizations don't have to choose — they run both. Here's how the platforms compare, and how Ridge IT deploys each in context.
| Capability | Okta Workforce Identity | Microsoft Entra ID | Ridge IT Guidance |
|---|---|---|---|
| Primary Use Case | Universal SSO across all apps — SaaS, on-prem, custom | M365 and Azure authentication, Conditional Access | Start with Entra for M365; add Okta for broader app coverage |
| Multi-Vendor App Catalog | 7,000+ pre-built integrations (SAML, OIDC, SCIM) | Strong for Microsoft apps; limited for non-Microsoft SaaS | Okta preferred when more than 10–15 non-Microsoft apps in catalog |
| Adaptive MFA | Risk-based, device trust, FastPass passwordless | Conditional Access + Microsoft Authenticator (requires E3/E5) | Both capable; Okta more policy granularity per-app |
| CMMC / FedRAMP Support | FedRAMP High authorized; GCC High Add-On for DoD | FedRAMP High via GCC High (M365 subscription required) | Ridge IT deploys both — Okta for identity, Entra ID for M365 integration — across FedRAMP and CMMC environments |
| Lifecycle Management | Full SCIM automation; HR-driven provisioning (Workday, BambooHR) | Strong within M365; third-party provisioning more complex | Okta preferred for cross-platform lifecycle automation |
| Identity Threat Detection | Okta Identity Threat Protection with Okta AI | Entra ID Protection (P2 required) | Both signal to Ridge IT SOC via CrowdStrike + Sentinel integration |
| Cost Model | Per-user subscription; tiered by feature set | Included in M365 E3/E5 or as Entra ID P1/P2 add-on | Entra often the lower-cost starting point if M365 licensed |
Ridge IT manages both platforms. Talk to a Pro about the right combination for your environment.
Common Questions
Okta Implementation & Identity Services — Frequently Asked Questions
Okta Certified Delivery Partner status verifies that Ridge IT has the technical expertise to architect, deploy, and manage Okta Workforce Identity solutions at scale — not just resell them. It requires demonstrated competency across SSO, Adaptive MFA, Lifecycle Management, and Identity Governance, and validates that our engineers have shipped real Okta deployments in production environments. Our team has delivered Okta at every scale, from lean mid-market rollouts to a 3-million-user consolidation for a Department of Defense-adjacent agency. See the full scope of our ICAM practice.
Ridge IT deploys and manages all four Okta Workforce Identity tiers — Starter, Essentials/Core, Professional, and Enterprise. This covers the full platform: Universal Directory, SSO, Adaptive MFA, Lifecycle Management, Access Governance, Privileged Access, Identity Threat Protection with Okta AI, Identity Security Posture Management, API Access Management, and Access Gateway. We also deploy the FedRAMP High Cell Add-On for defense contractors and government agencies. Contact us for a custom quote.
Okta is the identity control plane in a Zero Trust architecture. Every access request — regardless of network location — is verified against Okta's user identity, device posture, and risk signals before being permitted. Ridge IT integrates Okta with Zscaler ZPA for network-layer Zero Trust access and CrowdStrike for endpoint verification, creating a complete verify-before-connect posture. See our Zero Trust Architecture page for the full stack design.
Yes — when properly deployed. Okta's FedRAMP High-authorized platform satisfies multiple CMMC Level 2 and Level 3 access control and identification requirements, including AC.1.001 (limit access to authorized users), IA.3.083 (MFA for privileged accounts), and AC.2.006 (lifecycle management). Ridge IT's CMMC enclave architecture integrates Okta with Microsoft GCC High, Zscaler, CrowdStrike, and Azure Sentinel to address 110 of 110 CMMC controls. Visit our CMMC Compliance page for the full framework.
Yes. IdP migration is a core part of our Okta delivery practice — we've migrated organizations from Active Directory, Azure AD, legacy LDAP systems, and a mix of all three. Our crawl, walk, run migration methodology keeps production running throughout the process: we validate every SSO app connection in a pilot group before moving forward, and we only decommission legacy systems after full validation. For complex environments (multi-subsidiary, DoD enclaves, legacy on-prem applications), we scope individually. Schedule an assessment to discuss your migration path.
Yes. Most organizations run Okta and Microsoft Entra ID together — Okta as the primary IdP for SSO and Adaptive MFA, Entra ID for M365 authentication and Conditional Access. Ridge IT architects these systems to complement each other. For organizations already on M365 Business Premium or E3/E5, we frequently start by extracting full value from Entra Identity Protection and Conditional Access before recommending Okta for broader SSO coverage. See our Microsoft 365 managed services page.
CIAM (Customer Identity and Access Management) certification means Ridge IT has demonstrated expertise in deploying Okta's customer-facing identity solutions — not just workforce identity. This covers customer registration, progressive profiling, adaptive authentication for consumer apps, API access management, and fraud prevention. Organizations with customer portals, patient portals, partner extranets, or public-facing applications benefit from a CIAM-certified Okta implementation partner who understands both the security and user-experience requirements.
Timeline depends on scope, but most mid-market Okta implementations follow a 30-60-90 day phased approach. Phase 1 (Discovery): 2-3 weeks to map your identity environment, app catalog, and compliance requirements. Phase 2 (Core Deployment): 4-6 weeks for SSO, Adaptive MFA, and initial lifecycle rules. Phase 3 (Advanced Features): Governance, Privileged Access, CIAM, and cross-stack integrations. Ridge IT's crawl, walk, run methodology means you get production value in weeks — not months of architecture-only consulting. Schedule an assessment to scope your environment.
Sources & Methodology
- IDSA 2024 Trends in Securing Digital Identities (via BeyondTrust, 2024) — 90% of organizations experienced at least one identity-related incident in 2024.
- SpyCloud 2025 Identity Exposure Report — Identity-based attacks accounted for 64% of all incidents in 2024.
- Microsoft 2024 Security Report (via Parachute.cloud) — Password-based attacks accounted for over 99% of 600M daily identity attacks.
- IBM Cost of a Data Breach Report 2024 — Global average breach cost $4.88M.
- Ridge IT internal data — 3M-user federal agency Okta deployment supporting FedRAMP High and NIST 800-53 controls. Results may vary by environment and engagement scope.
Ready to Deploy Okta the Right Way?
Identity Is the Perimeter. Protect It.
Ridge IT's Okta delivery team is ready to assess your identity environment, map the right Okta services tier and architecture, and deploy your Okta implementation without disrupting your operations.
